Table of Contents
Many people use free proxies that are harvested from the Internet, in fact probably most people who use proxies use free proxies. Proxies are popular ways to hide your IP and are available on boh Mac, Windows, and various Linux flavors. And gamers, we got you covered with a Proxy Server for PS4. This site here is an example of one place where you might get the free proxies from and you can find many many more if you do a quick Google search for something like free proxy list. You can also check out Luminati proxy, Storm Proxies , or RSocks Proxy Review– some of the most reliable proxy networks. On the other hand, there are others designed more for businesses, as you can read in our Oxylabs Proxy review.
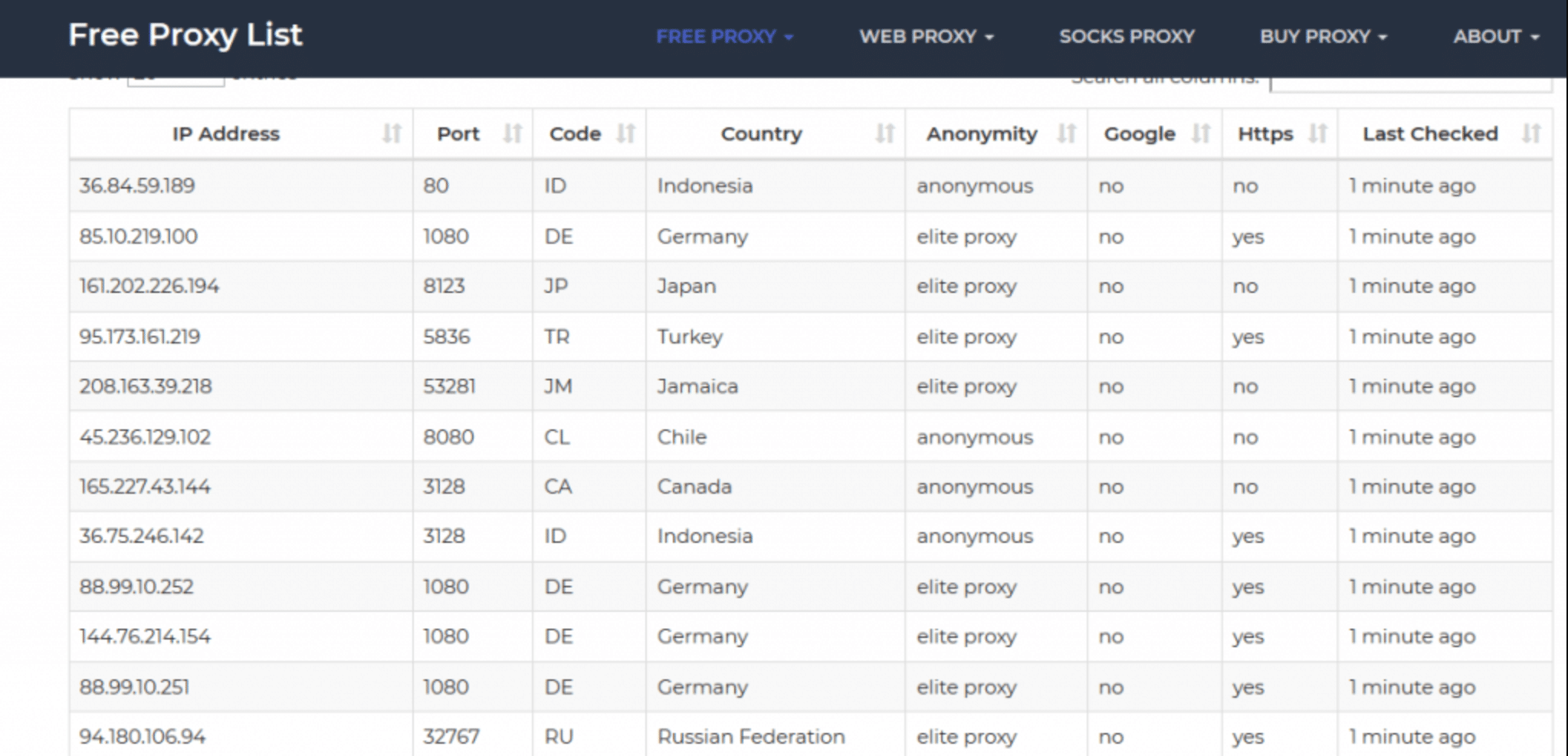
Below is an image of such lists and you see it states the IP addresses, the port, where it’s located, the type of server it is such as anonymous or elite, and whether you are going to get any problems with Google, whether it’s HTTP or HTTPS. So, you may ask – How do I check what my proxy server is? And in case you need help setting up a proxy server, or need an easy fix for the ‘unable to connect to the proxy server’ issue, click here.
The Types of proxies
There are basically 3 types of proxies which are
- Transparent proxies
- Elite proxies
- anonymous proxies
Transparent proxies which are also sometimes called “non” depending on the site are proxies that are not attempting to hide the user’s IP address or that you’re using a proxy from the destination. They send the HTTP Forwarded-For header which discloses your IP address and provides no level of anonymity at all. And then you’ve got Anonymous proxies that hide your IP address but does not hide from the destination that you are using a free proxy. The destination then could, of course, choose to block you based on the information. Next, you have the elite proxies which are sometimes called highly anonymous. These hide your IP addresses and hides that you’re using a free proxy from the destination.
On different sites these proxies could have slightly different names but generally, those are the three levels of the type of proxies that you will get. But because these are free there is no guarantee that this is accurate at all. For example an elite proxy that you pick could be using HTTP Forwarded-For header and forwarding your IP address. So if you are going to consider using these then you would have to use the sites that I’ve already shown you to check how the destination will see you using one of these proxies and determine if the proxy is providing any amount of anonymity. And here are a couple of sites [ Here and Here] to help you determine whether or not your IP address is being hidden and whether it’s a proxy that does not reveal that it is a proxy. So obviously you would need to first add your proxy to your application and then visit those sites
It would be trivial for a destination server to determine if an IP address was running a proxy or if it was set up to do so simply by scanning the ports or the server however that would be a heavy task for the server to do that for every connection but it is possible if that was something that a destination server was concerned about.
There are lots of proxy checking software that people can use to validate if the free proxies are live and working and there are online versions where you paste the proxies with there ip & ports and its checked and the live ones will be reported back. As well as online versions you can also download software to install on your operating system which will also do checks to see whether the proxies are live and anonymous. You’ll find many of the free proxies do not work and are extremely slow
Free Proxy Servers
So you might be wondering where all these free proxy servers are coming from and who runs them and why do they run them? Well, that’s a good question, almost all of these proxies are likely to be extremely dodgy. I’m not aware of a legitimate public free list HTTP/HTTPS and SOCKS proxies. This means the list of free proxy IPs you can find are very likely to be hacked machines, organizations or people that were silly enough to leave an open proxy on the internet, honeypots designed to observe you or even a bad actor wanting to do any number of attacks against you as a proxy is by its very nature a man in the middle so can attempt to do any number of attacks against you including SSL stripping and injecting code into your session to hijack your browser which is trivial if you are using HTTP and they are your proxy.
The proxies on many web sites will be found by the web site owners permanently scanning the internet for open proxies and when they find them they add them to a list like these. It may also be illegal for you to be using these depending on the laws of your country and the laws of the countries where the proxies are residing. Even if they are legitimate they can log all activities and forge your IP to the destination at any point they choose so they are not in any way a serious anonymising service. There are companies who sell lists of proxies and these are mostly again legally questionable and should be avoided. You’re asking for trouble deliberately placing an unknown something between you and your destination
Summary
Only use the free proxies if you have isolation from possible attacks such as sandboxing, live operating systems, virtual machines, and so on. Use these if your privacy and anonymity needs are just minor and there are small consequences. You can, of course, set up your own proxy server as a method of bypassing censorship or to change your IP address which I have talked about in the bulletproof hosting post. But to be frank, if you can set up a proxy, why not set up something better that supports encryption and is better for privacy and anonymity and security such as a VPN.
Proxies offer weak protection against the destination server knowing your IP address and it’s obvious to an observer that you are using a proxy service so they offer no protection against an adversary being able to observe your traffic. They should only be used as a last resort if privacy and anonymity is a minor need. You can chain multiple proxies together and that’s called proxy chaining which in theory gives you a little bit of anonymity.
FAQs
1. Is it good to have proxy server?
Yes. Proxies add an important layer of protection to your computer. They can be configured as web filters or firewalls, safeguarding your computer against online threats such as malware. Additionally, this additional security is beneficial when used in conjunction with a secure web gateway or other email security products.
2. Is it legal to use a proxy server?
Yes, using a free proxy server is legal. Proxies are useful for a variety of purposes, including enabling remote work, establishing a support operating system for internet users who are not connected to a specific virtual private network, protecting networks and Internet users from malicious content, and streaming online content from outside a country.
3. Can proxies steal info?
Proxy servers can be used to steal information by acting as a middleman between the user and the website they are trying to access. The proxy can capture all of the information that is sent between the user and the website, including passwords and credit card numbers. This information can then be used by the proxy server owner or sold to third parties.
4. Can proxy servers be traced?
Proxy servers can be traced, but it depends on how well they are configured. Generally speaking, most proxy servers can be traced back to the IP address of the server that they are proxying traffic through. However, some proxy servers are configured to obscure this information, making them more difficult to trace. In addition, many organizations use proxy servers to protect their internal networks from malicious actors, so tracing a proxy server can be difficult if the organization does not want it to be traced.
5. Is VPN better than proxy?
VPN and proxy are both technologies used for internet security and privacy. They both allow users to browse the internet anonymously and protect their data from being monitored or intercepted. However, there are some key differences between VPN and proxy.
Proxy servers are typically less secure than VPNs, because they do not encrypt your traffic. This means that your data can be intercepted and read by third parties.