11 Top Picks
4 Reviewers
32 Hours of Research
28 Options Considered
Whether you need the best packet sniffer or the best network analyzer, our comprehensive list will find them all for you. We understand how difficult it can be to find the right tools for your network, and IT professionals and System Administrators can get extremely busy when things go wrong.
They need tools they can rely on. That’s why our article is going to help you! We reviewed tons of different network packet sniffers and network analyzers and discovered our 11 favorite options. We’ve left you with their strengths and weaknesses, and talked a little about their features. In case you’re not a fan of these, we also tipped you off to some things to look for when making your selections.
Best Packet Sniffer and Network Analyzer Reviews
A lot of shoppers who look for reviews need something quick, so in case you don’t need our buyer’s guide we put that at the end. Here are the best packet sniffing and network analyzers on the market today!
3 Top Hardware Monitoring Software
1. WireShark
4.9/5
Wireshark is amazing! It has tons of great features and it’s completely free! This is a fantastic option for IT departments with budgetary constraints.
2. SolarWinds Packet Network Analysis Bundle
4.7/5
SolarWinds network performance monitor has a fantastic bundle that can handle nearly anything you need. This IT tool is extremely broad thanks to the bundle. When you collect network traffic and network usage using SolarWinds, it’s a very smooth and easy process.
3. Steel Central Packet Analyzer
4.6/5
River Bed’s Steel Central Packet Analyzer is great for anyone who needs to dive deep into packet details to solve their network issues. This network traffic analyzer tool is a great way to gain network visibility.
1. WireShark
4.9/5
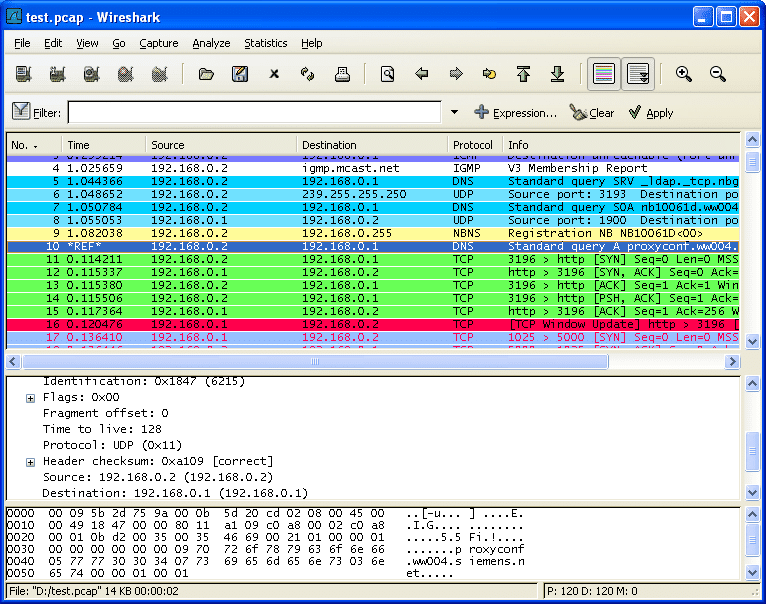
Wireshark is amazing! It has tons of great features and it’s completely free! This is a fantastic option for IT departments with budgetary constraints. It will log any network behavior that is problematic or unusual and allow you to view the data live and compare it to previously captures files for any changes.
The obvious fault in the system is that, when you are using an open source software, you don't have any formal documentation and there is no help desk to call when you run into issues.
The forums have tons of people willing to help answer questions, and there are tons of tutorials available, but at the end of the day, if an enterprise-level IT guru needs to pick up the phone and dial an 800 number for an immediate response to an emergency, they can't do that with Wireshark.
That being said, the advantages to open source software more than make up for that. Wireshark has the most active community of developers available when it comes to open source software.
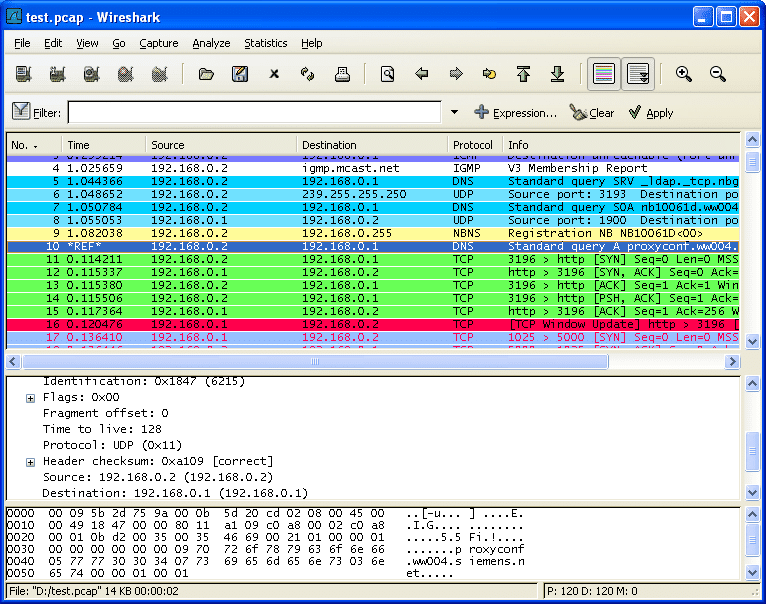
This includes tons of extremely knowledgeable and very active forum users who can answer your questions pretty quickly.
The system includes a filtering system and a macro system. Both of them are extremely powerful. Wireshark lets you view tons of different statistics, too. You can track your conversions, endpoints, and network protocol hierarchy effortlessly.
You can also perform analyses for VoIP, capture Read/Write in a variety of different formats, and export your results to CSV, PostScript, XML, or plain text! It even supports decryption and coloring rules.

WireShark Pros
WireShark Cons
2. SolarWinds Packet Analysis Bundle
4.7/5
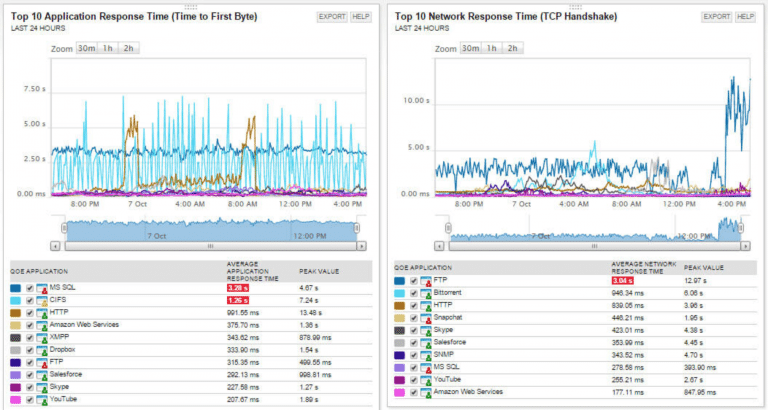
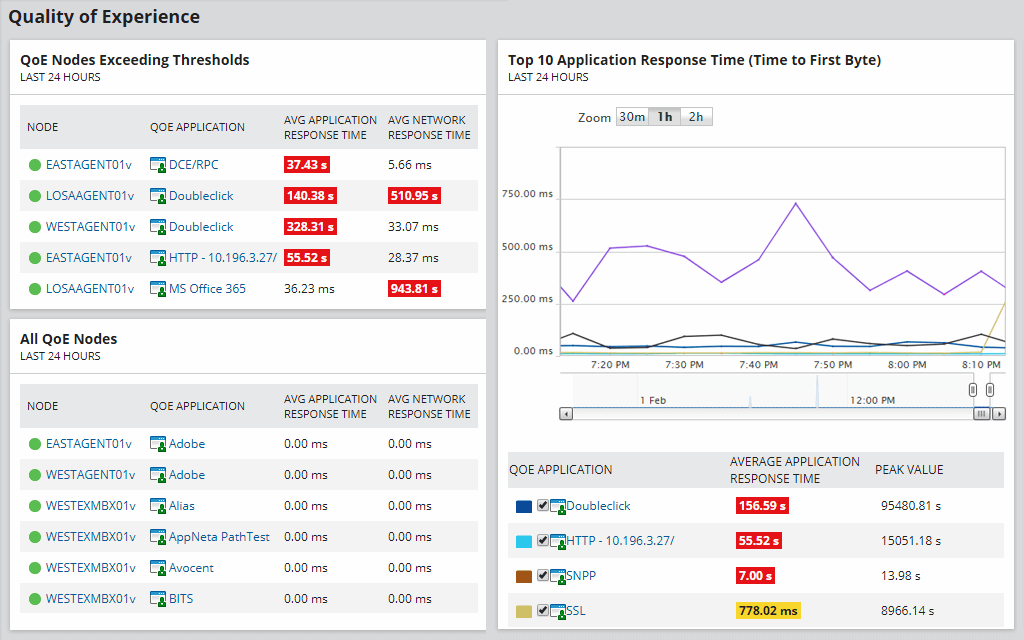
SolarWinds has a fantastic bundle that can handle nearly anything you need. This IT tool is extremely broad thanks to the bundle. When you collect network traffic using SolarWinds, it’s a very smooth and easy process. It even offers beautiful reports, with tons of details and simple graphs so you can present your network analyses to the management teams who don’t understand tech.
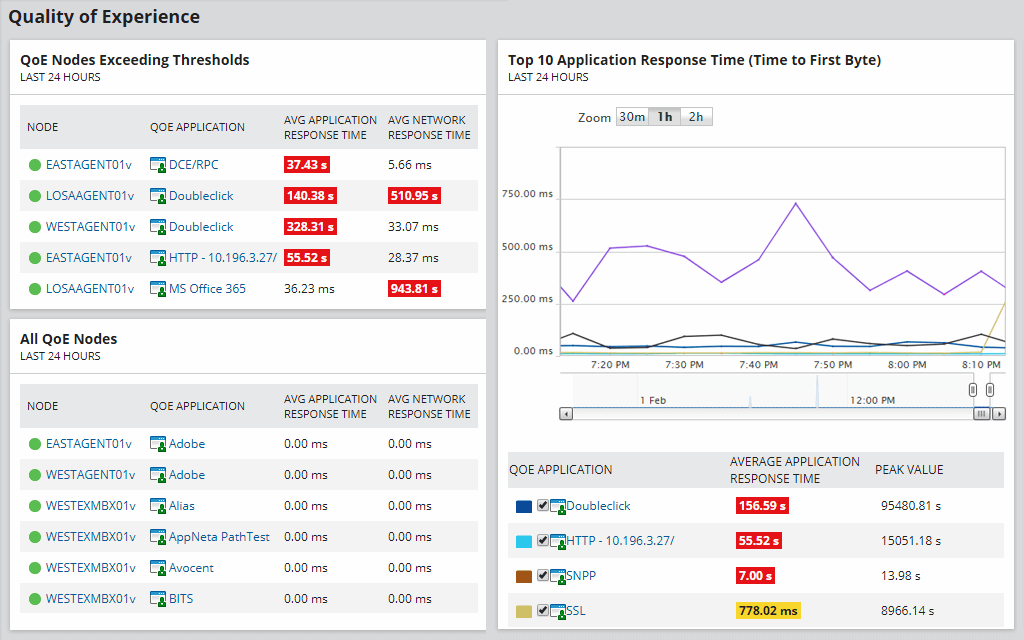
There are a few downsides, though. SolarWinds can hog a lot of resources and it can be prohibitively expensive for a lot of smaller businesses. Even the beautiful graph feature has a drawback because you can’t download PDF versions of them.
SolarWinds is extremely powerful. Tons of massive, strong IT departments rely on it regularly. Their reporting system is extensive, so you can see everything, including which traffic volume is prohibitive to production.
You can see your traffic volume at every given moment and fix issues quickly. It is very easy to set up and get working and allows for a very detailed history, so you can troubleshoot when problems arise and differentiate between normal behavior and abnormal issues.
Although it is costlier than other solutions, it’s one of the best cost to benefit rations there is in this line of work. It provides critical information about your network that metadata alone won’t show you thanks to the Deep Packet Inspection.

This means the information you receive will actually be insightful. They allow you to identify traffic by type or category and set a risk level for each, which can help you eliminate traffic issues and filter out problems and intrusions quickly.
SolarWinds Packet Analysis Bundle Pros
SolarWinds Packet Analysis Bundle Cons
3. Steel Central Packet Analyzer
4.6/5
River Bed’s Steel Central Packet Analyzer is great for anyone who needs to dive deep into packet details to solve their network issues. This network analyzer tool is a great way to gain network visibility. It has one of the nicest user interfaces (UI) imaginable. It’s an incredibly easy portal to use!
A lot of different tools can be integrated so effectively that users can simply drag and drop what they want without needing to type in any command lines. It’s got tons of great features and can perform analytics of nearly any kind.
It also monitors the experience and network activity at every scope of magnitude, allowing you to discover problems quickly and easily find solutions. It has more data sets than most people ever need to use along with the analytics to go with them.
It allows you to take control of your network traffic on a micro level and predict and prevent future problems. It is also able to handle large files, so if you need to capture more than 2 gigs of data, this is your best bet. It runs quickly and allows you to use your tools without programming command lines.
If you have repeated network abuses, this is a good tool for you. The monitoring works very well, so you can look at specific end users and see exactly how they make use of the network.

This lets you remove access to certain things if users are abusing the network and limit their use if they’re hogging more than their fair share of resources.
Steel Central Packet Analyzer Pros
Steel Central Packet Analyzer Cons
4. EtherApe
4.4/5
EtherApe is unique because it is a graphical network performance monitor. This is an especially great option for visual people and for presenting network data to management. It is very clean and easy to use, with a UI as simple as their advanced network traffic analysis charts.
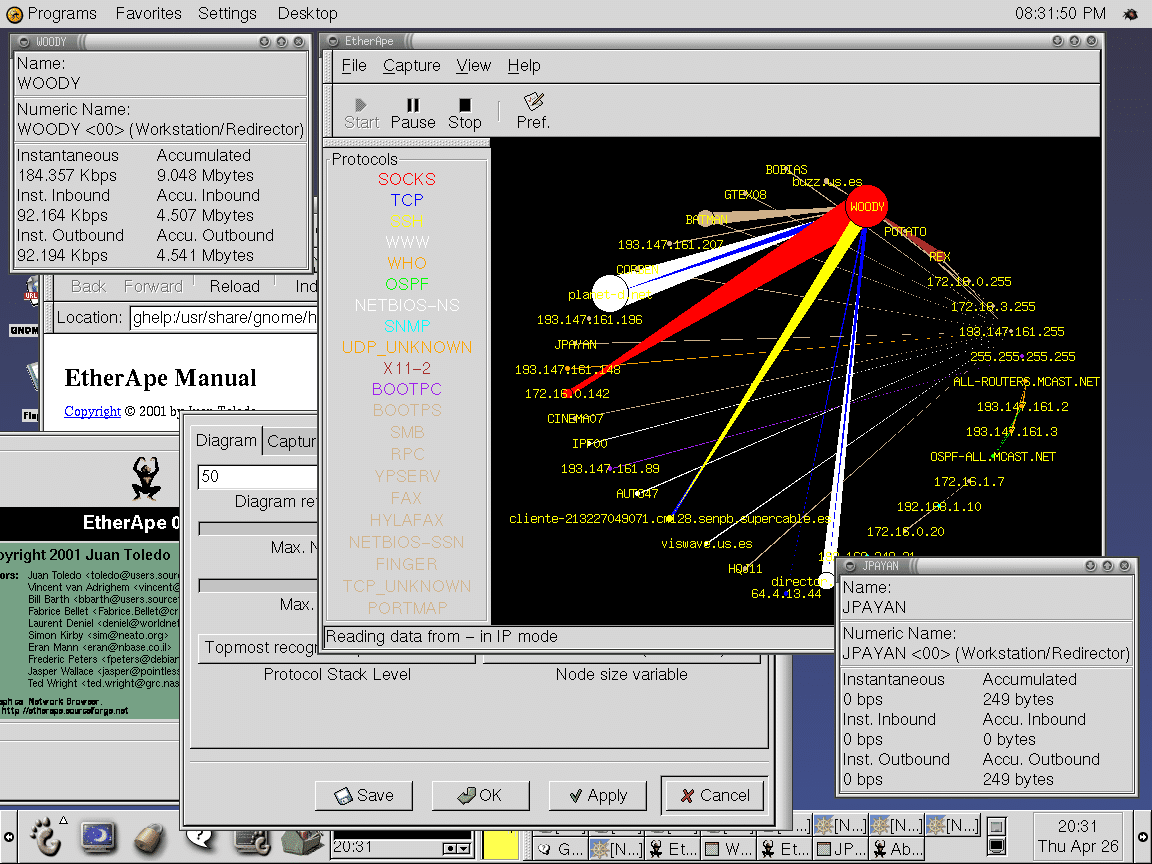
The ability to get instantaneous feedback is really cool. With EtherApe, you can just use a managed switches monitoring port to watch your traffic flow in real time. This is the best way to see what’s happening on your network!
This network monitoring tool has a ton of great features, too. Nodes and link colors will show you what network protocols are being used most frequently. You can select the level you want to concentrate on, allowing you to fix a specific network protocol stack if it is especially problematic.
This allows you to see your network traffic, but it also lets you monitor traffic going through end to end IP or passing from TCP port to TCP port.
You can capture and collect your network data from a live connection then read it later thanks to tcpdump capture files. The live data can be accessed and read through the Ethernet, SLIP, FDDI, WLAN, and PPP interfaces. It supports a massive amount of frame and packet types, too!

This system also allows you to customize your data displays using the pcap syntax in the network filters. You can display your averages, your node persistent times, and more, and all of these are completely customizable so you can configure them however you want to.
EtherApe Pros
EtherApe Cons
5. KisMAC
4.4/5
If you own a Mac, then you should look into KisMAC. It will map your wireless networks then provide statistics and data about their performance, making it easy for you to troubleshoot any issues.
KisMAC is a great tool for people who want to audit their networks and do performance monitoring. It excels at testing the security of your Wi-Fi connection.
Although it doesn’t have centralized support, there are tons of tutorials, injection packets, and FAQs in their very active online community so you should get your answers quickly.
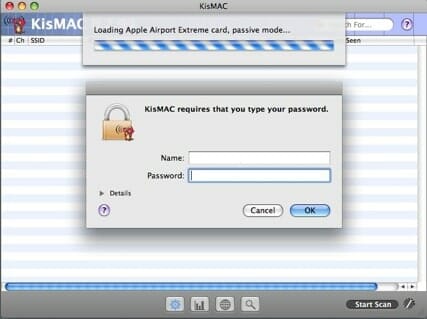
KisMAC Pros
KisMAC Cons
6. PRTG Network Monitor
4.2/5
Paessler’s PRTG Network Monitor is another very popular option. As a network performance manager, it is a great tool for managing your infrastructure and it can also monitor your network for you. It’s flexible enough that both large and small companies could easily make use of the network management software in their workplace.

This tool focuses on monitoring, making it one of the most extensive options available for monitoring your network right down to the individual network devices that use it. It provides a perfect network monitoring service with a unified way to manage infrastructure.
Businesses can have up to 100 sensors for the free version, so it would be easy to conduct an evaluation. You can monitor all of your routers, access points, switches, and could and software infrastructure easily.
This includes services, storage, servers, and apps. Even work stations can be added to the monitoring without making things too complicated.
The tool went through a significant revamp in late 2018. This enhanced the performance and improved the user interface (UI). The dashboard got a sleeker, user friendly look that offers displays and graphics for analytic symbols instead of the older version. This allows you to have more information without the clutter.

It responds very well, too. The tool is smart enough to immediately optimize to any device that you access it from, so you don’t have any issues. It has a great option to set alerts for anything that you are monitoring, so you will know the instant something deviates from the norm. It is also extremely flexible.
PRTG Network Monitor Pros
PRTG Network Monitor Cons
7. Fiddler
3.6/5
Fiddler is a completely free web debugging proxy that is compatible with any platform, system, and browser. This allows you to trap undesirable network traffic between the Internet and your test computers so that you can inspect all of the data that is outgoing and incoming and monitor it.
On top of monitoring data, you are also able to modify requests and responses before the end user’s browser can receive them.
It even offers an extremely powerful scripting subsystem that is based on events, so you can tweak it to do a lot of different things. You can even extend it by including .NET Framework language commands.
The HTTP replay option with Fiddler allows you to troubleshoot issues from the client side.
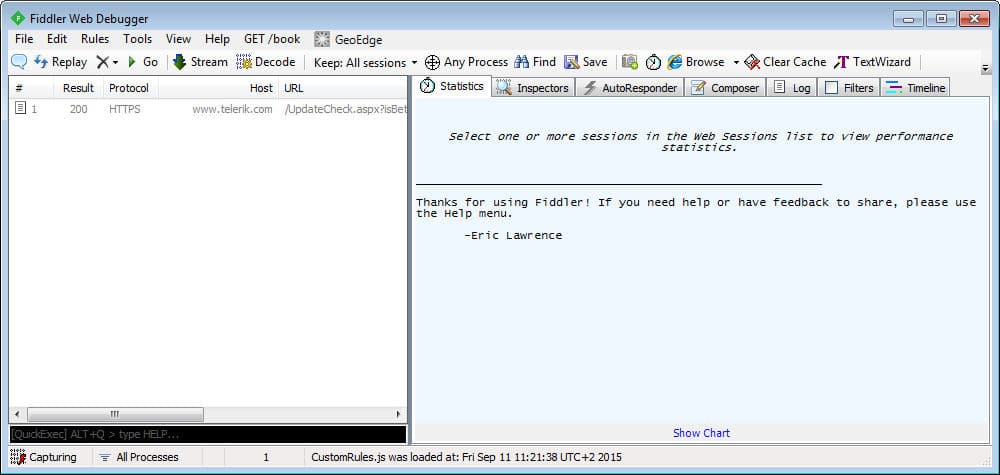
All you need to do is make an offline copy of the site you’re testing then use the tools to make offline images for packaging and network performance analysis. This allows you to see anything you need to in order to debug your system.
Fiddler can handle HTTPS issues with a single click. It’s a great way to spy on any encrypted traffic hitting your network without needing to install anything extra.

It’s filled with tons of amazing features and even professional IT and Network Administrators rarely use 95% of the things Fiddler is capable of performing.
Fiddler can easily edit web sessions and record service requests and data. You can configure it so that it will decrypt everything or set it only to decrypt specific sections of the network. You can troubleshoot JavaScript errors and see the entire page weight when it comes to caching HTTP and compressing it. You always know you’ve got the right cookies and cache directives being sent from the client to the server.
Fiddler Pros
Fiddler Cons
8. Packet Capture
3.5/5
Paessler’s Packet Capture tool is a great packet sniffing tool. It provides an infrastructure monitoring tool that is completely unified. This will allow you to manage your network and servers easily.
The Paessler Packet Capture tool can handle analyses of a lot of different functions. The packet sniffer will catch the headers of any network packets that come and go through your network, which makes it one of the fastest analysis tools on the market.
This also prevents the tool from taking up too much space when storing and holding capture files for you to use. The clean dashboard will categorize all your traffic by the type of application, including web packets, emails, chat app data, and the volume of any file transfers.
Packet Capture Pros
Packet Capture Cons
9. Tcpdump
3.4/5
Tcpdump is a bit of a beast. It is probably the least user friendly option available because it requires an in depth knowledge of TCP in order to work. The learning curve is very steep and intimidating enough that a lot of network administrators immediately dump it in favor of easier and more under friendly options.
That being said, if you know what you’re doing and have the experience to work with this system, it’s fantastic.
Tcpdump allows you to learn about the network traffic on your machine. Tcpdump is an extremely accurate network picture that will offer you recording and instantaneous insight into your activity. You can even save your PCAP files, which you can then export into a network analysis tool available because they are all compatible with PCAP files.
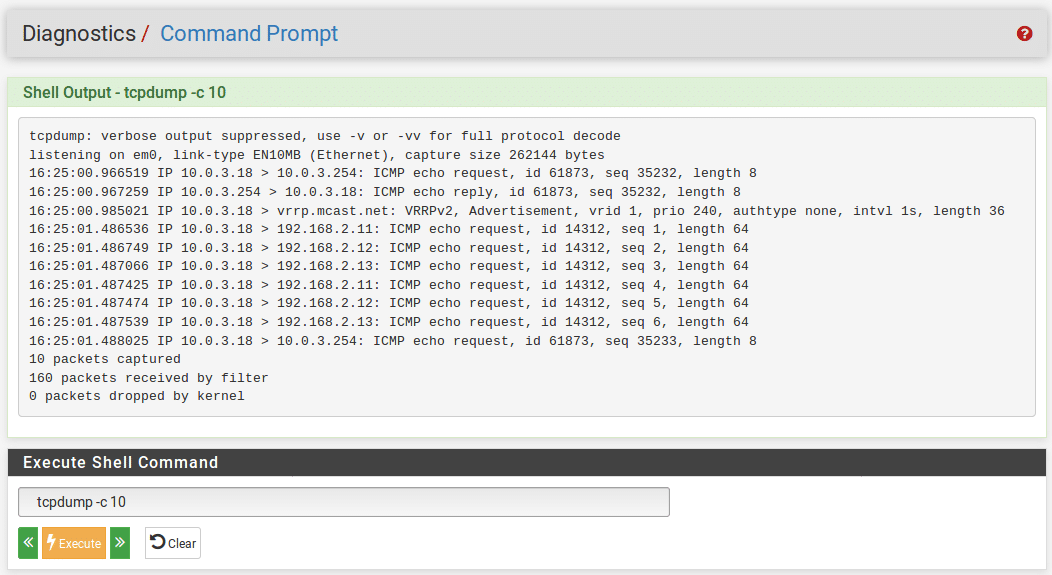
The tool also allows you to set a lot of custom flags and filters. You can easily filter the data that gets analyzed by IP address, Boolean queries, specific ports, or more!

One of the weaknesses of tcpdump is that, unlike Wireshark, it doesn't have the ability to look inside your packets. Still, it is incredibly useful for people who want to use it, and it has a ton of great enhancements that can be added to the basic software.
Tcpdump Pros
Tcpdump Cons
10. Kismet
3.4/5
Kismet is a great 802.11 layer2 wireless network analyzer app that offers sniffing and detection of intrusions. It works with any wireless card that can support raw monitoring (rfmon) and if you have the right hardware it can sniff out a lot of different types of traffic.
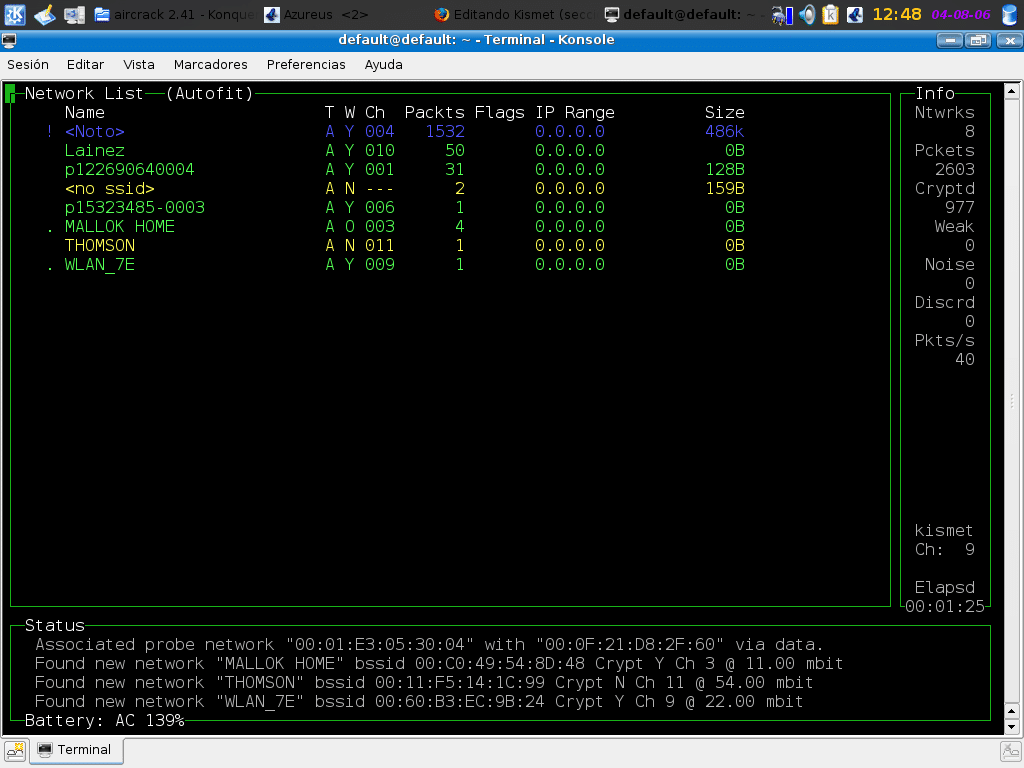
Kismet can detect any network, even if it is hiding itself through disabled SSID. This process works because Kismet will scan every channel in its frequency bad.
This is a passive packet sniffer, so you need to set a mode for Monitor functions. When you use it, Kismet can detect the hidden networks and display them.
This feature allows you to see the Access Point o(AP) of any network in the range, grab the MAC address (BSSID), the network name (SSID), the type of encryption being used, the channel it’s on, and how many packets it is sending and receiving in the network.
It can even determine when the network was last visible and fetch the MAC addresses of any clients that Kismet has tied to a specific Access Point. It’s a great way to audit any wireless networks, learn the different configurations being used, and identify the networks. It’s a great way to audit any wireless networks, learn the different configurations being used, and identify the networks.
You can see whether someone has configured a network incorrectly and detect unauthorized Access Points. The tool will show you how much bandwidth you’re using and let you save the captured packets in a file that is compatible with other analysis tools.

Kismet Pros
Kismet Cons
11. Network Miner
3.1/5
Network Miner was created as an open source tool for Network Forensic Analysis (NFAT) for Windows, but it also plays well with Linux, Mac OS X, and FreeBSD, so you have some options for implementation.
The free version has some great stuff if you’re on a budget. It can handle live sniffing, parsing both PCAP and PcapNG files, and extracting tons of files from IMAP traffic, POP3, FTP, HTTP, TFTP, SMB and SMB2, and SMTP.
It offers IPv6 support, can extract X.509 certificates from traffic that has been encrypted with SSL (like SMTPS, IMAPS, HTTPS, POP3S, FTPS, and more) and can receive PCAP over IP. It can decapsulate GRE 802.1Q, VXLAN, PPPoE, MPLS, OpenFlow, EoMPLS, and SOCKS. It even contains OS fingerprinting.
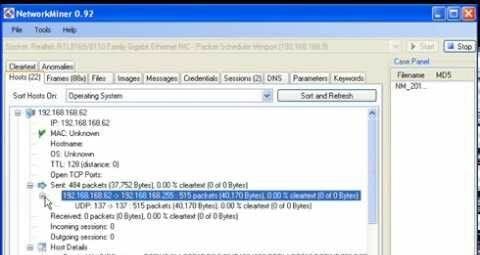
The Pro version is going to be pretty pricey, but it comes with an insane number of tools. On top of everything the free version offers, it also has the ability to extract audio and play it back form VoIP calls, look up the OSINT of file hashes, domain names, IP addresses, and URLs, and export to CSV, XML, CASE, JSON-LD< and even Excel.
It utilizes Port Independent Protocol Identification (PIPI) and allows the user to define their own Port to Protocol Mappings. You can configure output directories and your time zone, using either UTC or a local or custom time, and it includes geo IP localization.

You can whitelist DNSD, the OS fingerprinting becomes more advanced, and this allows you to trace web browsers. It comes with the detection of online ads and trackers and can host coloring support. It also has a command line script capability.
Network Miner Pros
Network Miner Cons
Buying Guide for Packet Sniffers and Best Network Analyzers
Now that you’ve heard our opinions when it comes to the best packet sniffer, it’s time for you to look for your packet analyzers and a network sniffer. Here are a few more things you might need to know before making your selection.
What is a packet sniffer?
A packet sniffer is a tool that administrators can use to monitor their network’s traffic. These will examine the data packets that pass from computer to computer or from the Internet to computer and give them a real time picture so that they can figure out where network clogs come from and troubleshoot problem areas.
Advantages of Packet Sniffing Software
Using a packet sniffer tool has some great advantages. These tools will allow you to implement a policy that limits and sets your company’s network capacity. These will pinpoint areas and links in the network that are extremely congested. They will also provide the statistics that will let you find the applications that are generating the highest traffic volumes. These tools also collect data so they can predict your network behavior, and will highlight your highest and lowest times when it comes to traffic demands.
Your budget will determine what you can do with that information. You can increase your network’s capacity if you have the available resources, but the packet sniffer also allows you to target new resources with efficiency. If you don’t have a budget, then the packet sniffers will allow you to prioritize your traffic, which can shape traffic, reschedule events that require a lot, limit the bandwidth of network hogs, and find more efficient alternatives to network hogging apps.
What is a network analyzer?
Network analyzers are tools that will capture any of the packets that are transmitting through a network so they can be inspected. These are also called packet sniffers. They can decode protocols so that humans can understand the traffic and store packets so that network administrators can analyze the data sets and compare them. They usually analyze packets in real time and help you analyze network performance.
Network Traffic Types
A network traffic analyzer can show you the different types of traffic. To analyze it properly, you will need someone who understands how networking occurs. None of the tools can remove the need for a network analyst that can use the information the tool gives you. For example, the average person won’t understand what a three-way handshake over TCP is, never mind how to use it to initiate connections between devices.
Analysts will need to understand that there are a variety of different traffic types in any network, including DHCP and ARP. The network analyzer software can show you what you ask for, but you will need to know what to ask to use and understand the types of network traffic. This knowledge is essential to make sure that you differentiate problems from normal network traffic.
Enterprise Tools and Hacker Tools
Enterprise networks are massive, so you will need massive tools to handle them. Enterprise tools are able to do comprehensive analysis beyond just the typical tcpdump. These tools allow you to correlate traffic from different servers, receive notifications for exceptions to typical traffic, automatically create graphs to display information for managers and non-network people, and even allow for intelligent query tools that can hunt for issues and save you time.
Hackers use packet sniffers, too. Packet sniffers can solve a lot of great problems in the hands of a competent hacker. Just remember that crackers (or people who are hacking with the purpose of doing harm or attacking) can also use them. Wire tappers are a great standby of people who want to steal your data while it is between nodes (wiretapping) or attack and change the data that is moving, which can divert your traffic, defraud a network user, and replace data with malware and viruses. Intrusion detection by using network security software can protect against unauthorized use.
FAQs
Enter your text here...
1. What is the best packet sniffer?
Here are Top 3 Hardware Monitoring Softwares that we can recommend.
1. WireShark - Wireshark is amazing! It has tons of great features and it’s completely free! This is a fantastic option for IT departments with budgetary constraints.
2. SolarWinds Packet Network Analysis Bundle - SolarWinds has a fantastic bundle that can handle nearly anything you need. This IT tool is extremely broad thanks to the bundle. When you collect network traffic using SolarWinds, it’s a very smooth and easy process.
3. Steel Central Packet Analyzer - River Bed’s Steel Central Packet Analyzer is great for anyone who needs to dive deep into packet details to solve their network issues. This network analyzer tool is a great way to gain network visibility.
2. What is a packet sniffer used for?
A packet sniffer, alternatively referred to as a packet analyzer, protocol analyzer, or network analyzer, is a piece of hardware or software that is used to monitor network traffic. Sniffers operate by examining data packet streams that flow between computers connected to a network, as well as between networked computers and the larger Internet.
3. Is packet sniffing legal?
In general, packet sniffing is legal. However, there are some specific cases where it is not. For example, if you are sniffing packets to gain unauthorized access to a computer or network, that is illegal. Additionally, if you are intercepting communications that are not meant for you, that is also illegal.
4. What are three components of a packet sniffer?
A packet sniffer is a program that intercepts and logs traffic passing over a network. It can capture information such as the source and destination of packets, as well as the payload.
There are three main components to a packet sniffer: the packet capture engine, the user interface, and the logging module. The packet capture engine is responsible for capturing packets, while the user interface allows you to view and analyze the captured data.
5. How does a packet sniffer work?
A packet sniffer is a tool that intercepts and logs traffic passing over a network. It can be used to capture packets for analysis or to troubleshoot network problems.
Most packet sniffers work by installing a special piece of software on a computer that is connected to the network. This software monitors all traffic passing through the computer's network interface card (NIC), and logs the data packets it intercepts.